Der globale Standard für digitale Konnektivität und intelligente Gebäude
Das Ziel von WiredScore ist es, Gebäude auf der ganzen Welt intelligenter zu machen und besser miteinander zu vernetzen.
Über WiredScore
WiredScore bewertet, zertifiziert und verbessert die digitale Konnektivität sowie intelligente Technologien von Wohn- und Bürogebäuden und unterstützt Projektentwickler und Bestandshalter im Umgang mit Gebäudetechnologie. Als globales Zertifizierungsunternehmen ist WiredScore in Nordamerika, Europa, Nahost sowie im Asiatisch-Pazifischen Raum vertreten.
Zertifizierte Gebäude
WiredScore hat global über 4000 Gebäude zertifiziert.

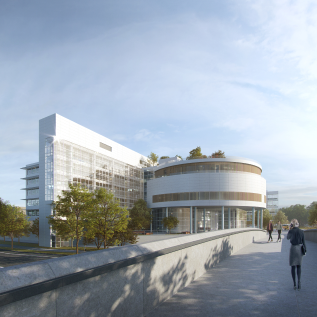
XRL Topside (Express-Rail-Link) West Kowloon Station
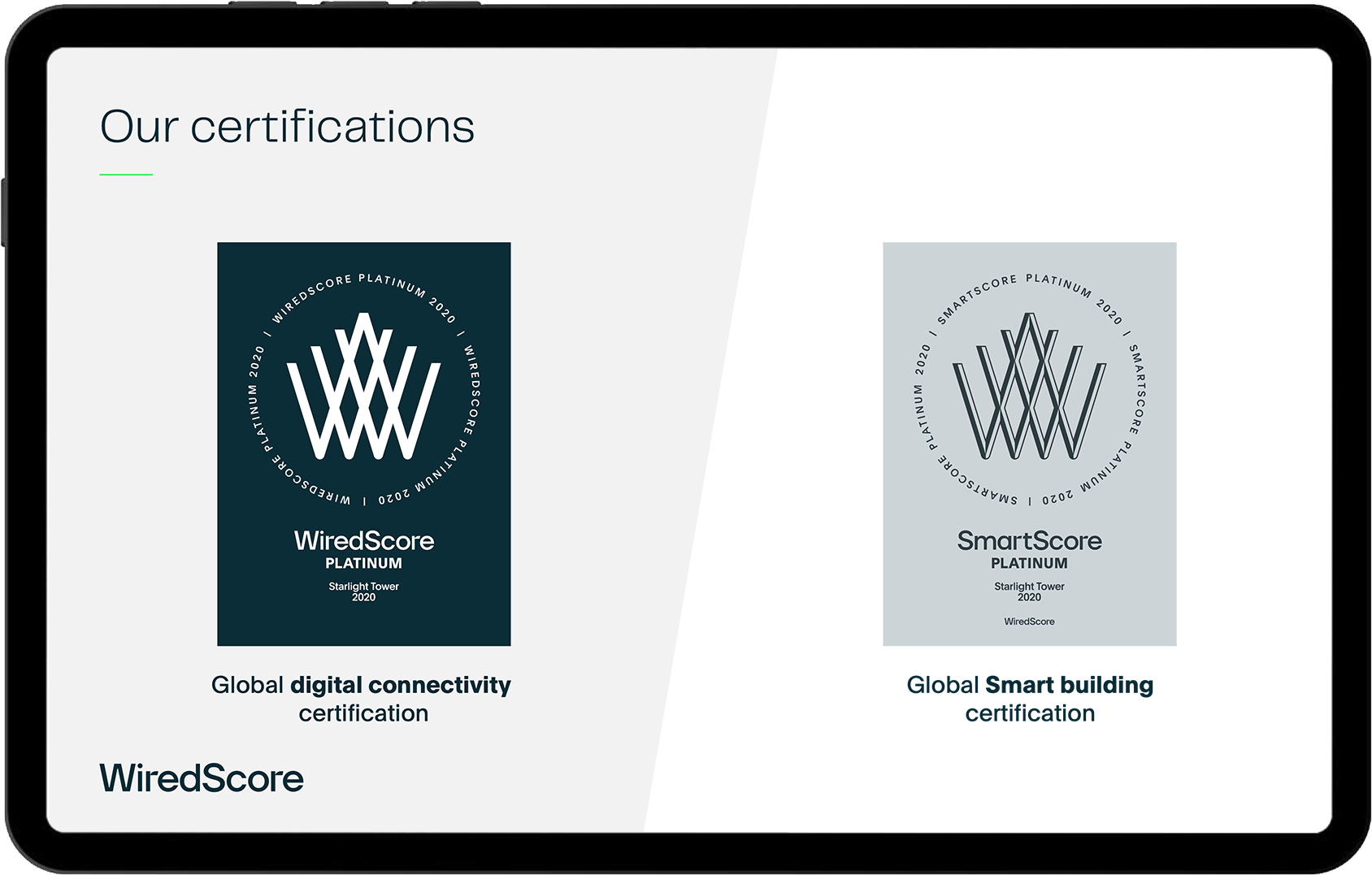
Unsere Zertifizierungen
WiredScore Zertifizierung

Die WiredScore Zertifizierung ist das Bewertungssystem für digitale Konnektivität von Büro- und Wohnimmobilien. Sie ermöglicht Bestandshaltern und Projektentwicklern die digitale Infrastruktur ihrer Gebäude zu verstehen, zu verbessern und zu vermarkten.
SmartScore Zertifizierung

Mithilfe der SmartScore Zertifizierung für Bürogebäude können Projektentwickler und Bestandshalter die Benutzerfunktionalitäten und technologischen Grundlagen ihrer smarten Gebäude gezielt optimieren und vermarkten.
Wollen Sie mehr erfahren?
Wenn Sie einen vollständigen Überblick über die Produkte von WiredScore erhalten möchten, können Sie die Produktpräsentation hier einsehen. Gerne können wir einen Termin vereinbaren um Ihnen die Inhalte vorzustellen.
Zertifizierungsgebühren
Die Zertifizierungsgebühren sind eine einmalige Gebühr und jeweils zu Beginn der Zertifizierungslaufzeit fällig. Die Gebühren starten aktuell bei 5.300 € netto für Bestandsgebäude bzw. 14.700 € netto für Projektenwicklungen. Die Gebühren sind abhängig von der Art der Zertifizerung und der Größe und Struktur des Gebäudes. Gerne erstellen wir ein unverbindliches Angebot. Hierfür benötigen wir die Adresse des Gebäudes und die Bürofläche (gif oder BGF) bzw. Anzahl der Wohneinheiten.
Unsere Partner

WiredScore’s Accredited Professsionals
WiredScore’s Accredited Professionals (APs) begleiten als Berater den Zertifizierungsprozess auf Kundenseite. APs haben ein Training bei WiredScore durchlaufen haben Erfahrung in der Anwendung der WiredScore und SmartScore Zertifizierung und den dahinterliegenden Kriterien.

WiredScore’s Accredited Solutions
Accredited Solutions sind Technologieanbieter, deren Systeme und Lösungen mit den Anforderungen der SmartScore Zertifizierung abgeglichen wurden und Mehrwerte für zertifizierte Gebäude bieten.
Neuigkeiten und Studien